Documentation Index
Fetch the complete documentation index at: https://docs.zeotap.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Source Access Rules let admins control which data sources — and optionally which specific attributes within those sources — are available when building audiences or journeys in a given folder. This is useful when you have sources that contain a mix of safe and sensitive data. Rather than making the entire source off-limits, you can make it broadly available but block only the sensitive fields in contexts where they shouldn’t be used. For the broader governance model — including how Source Access Rules relate to Folder Access Control and Mandatory Templates — see Access Rules.Composable Sources. The Join Key in sources tagged as Customer Parent Model cannot be restricted in any folder. This is because it is the foundation that enables profile unification — restricting it would break identity resolution across the org.
When to use Source Access Rules
Block sensitive attributes from specific teams. Your CRM source contains email, transaction history, loyalty tier, and national ID. Your marketing teams need email and transactions to build campaign audiences. They do not need national ID. You can block the national ID attribute from the marketing folders while keeping the rest of the source fully accessible. Restrict an entire source to specific contexts. You have a source containing medical or financial data that should only be accessible to a compliance-approved folder. You can block the entire source from all other folders, ensuring it only appears in the right context. Enforce data minimisation. Different teams should work with the minimum data necessary for their use case. A growth marketing team running acquisition campaigns doesn’t need loyalty or retention attributes. Blocking those attributes from the acquisition folder keeps the data environment clean and reduces the risk of misuse. Meet regional data requirements. Certain attributes may be permissible in one market but restricted in another. You can apply different rules to region-specific folders — for example, blocking a sensitive field from your Germany marketing folder while keeping it accessible in other markets.How Source Access Rules work
Default state
By default, every source — both new and existing — is available across all folders. No restrictions are applied unless an admin explicitly configures them.Access Rules cannot be applied to Archive folders.
Attribute-level control
Admins can either select all attributes from the source or select specific attributes within it.- Only the explicitly selected attributes are blocked in the targeted folders.
- All other attributes from that source remain fully accessible in those folders.
- For any new folder created after the rule is set, the source is fully accessible — including the otherwise blocked attributes. The new folder must be explicitly added to the rule for attribute restrictions to apply.
- Any new attribute mapping added to the source after the rule is set is accessible in all folders by default. It is not automatically blocked unless explicitly added to the rule.
Configure Source Access Rules
Create a Source Access Rule
Open the source
Navigate to Sources and open the specific source you want to configure an access rule for.
Open the Access Rule tab
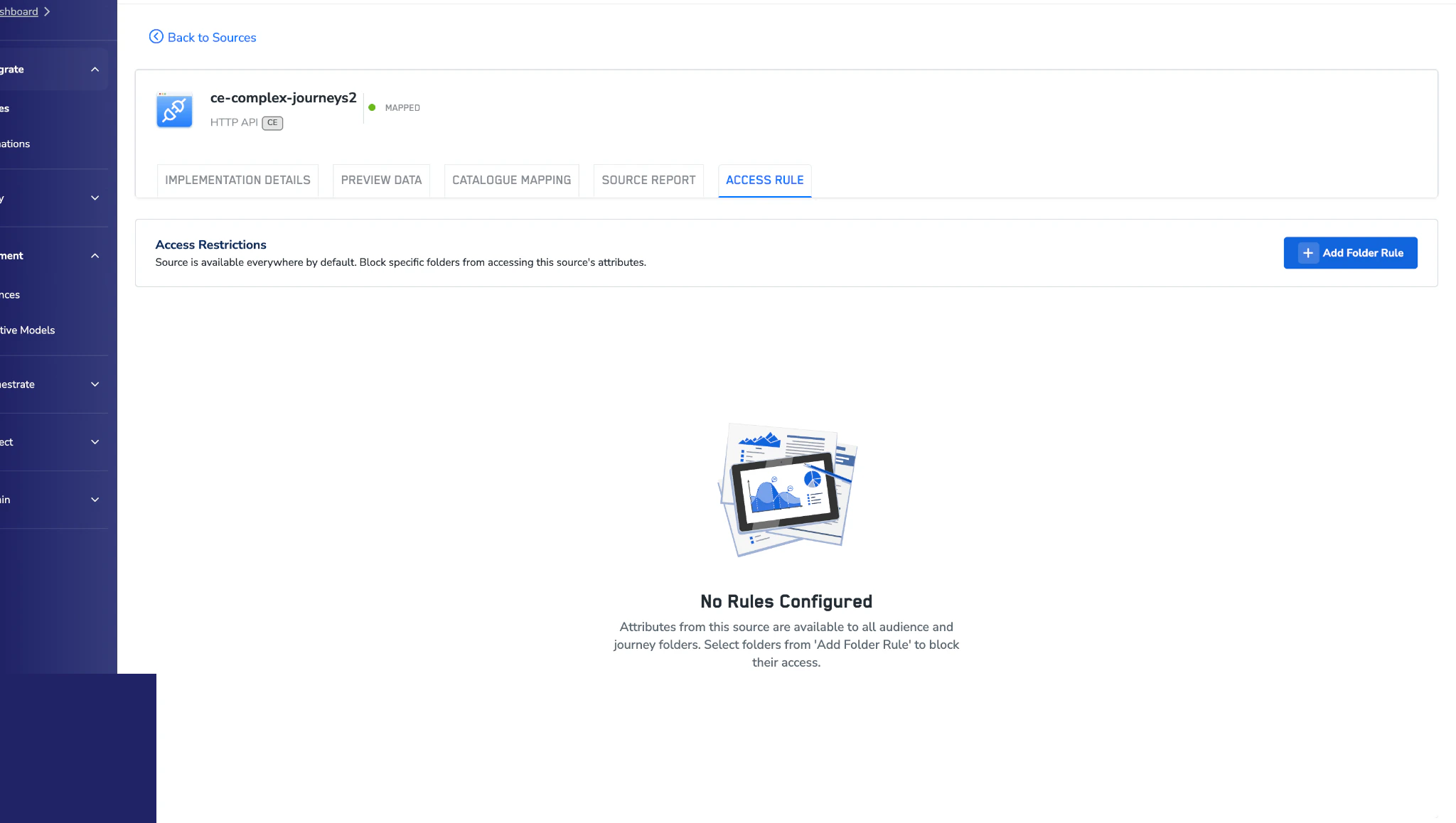
Select the Access Rule tab. If no rules exist yet, you’ll see the No Rules Configured empty state.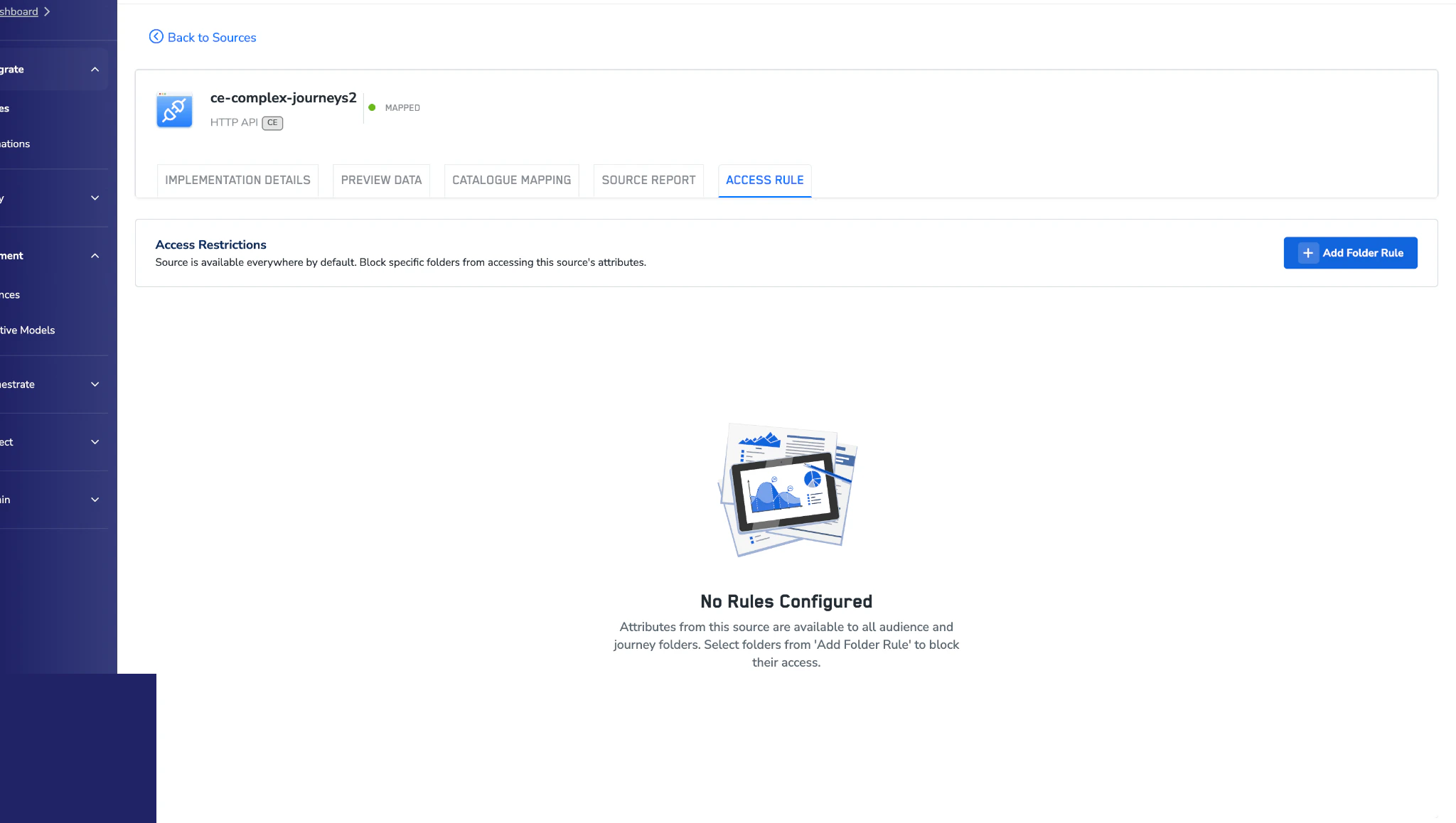
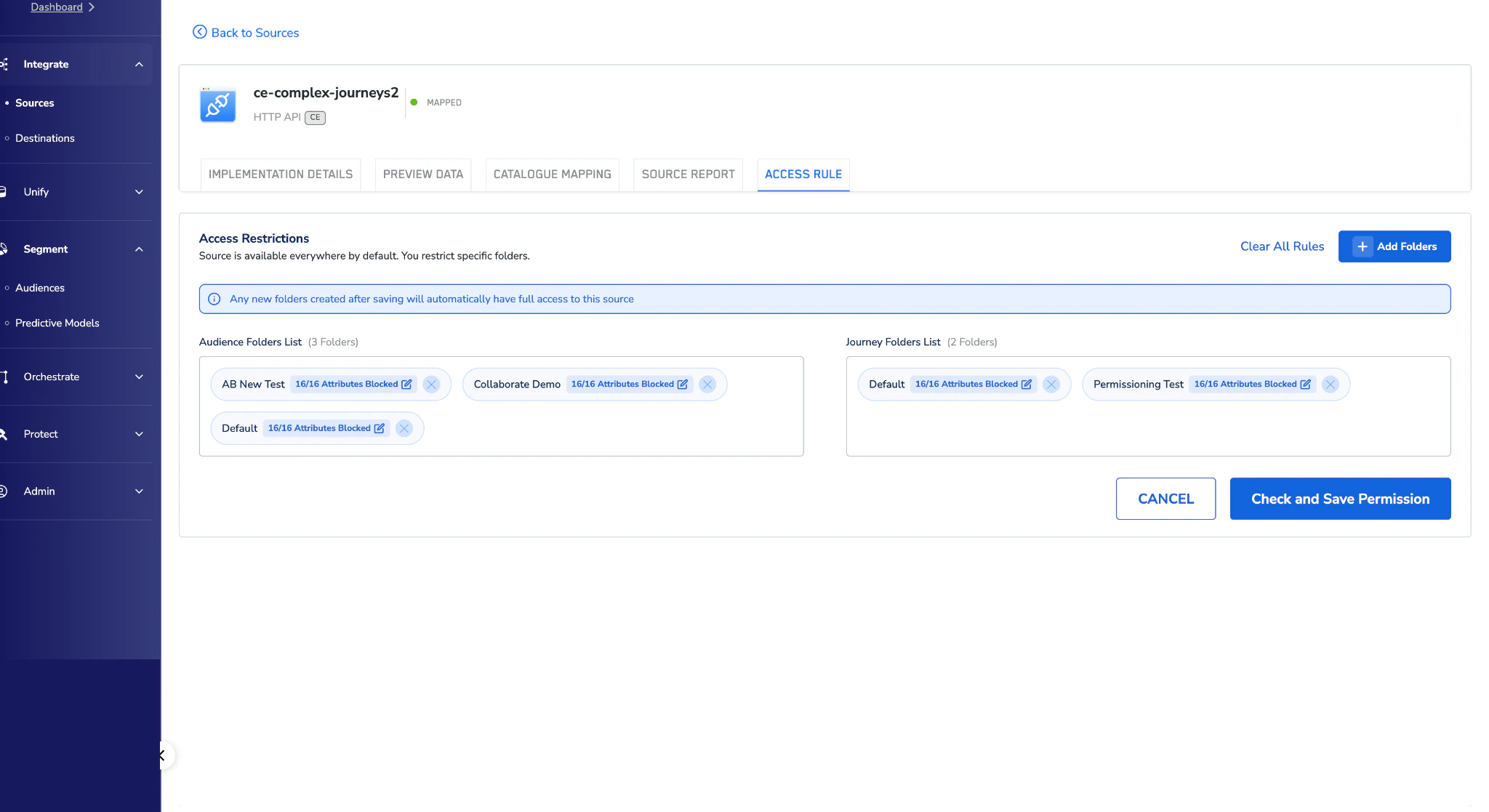
Add a folder rule
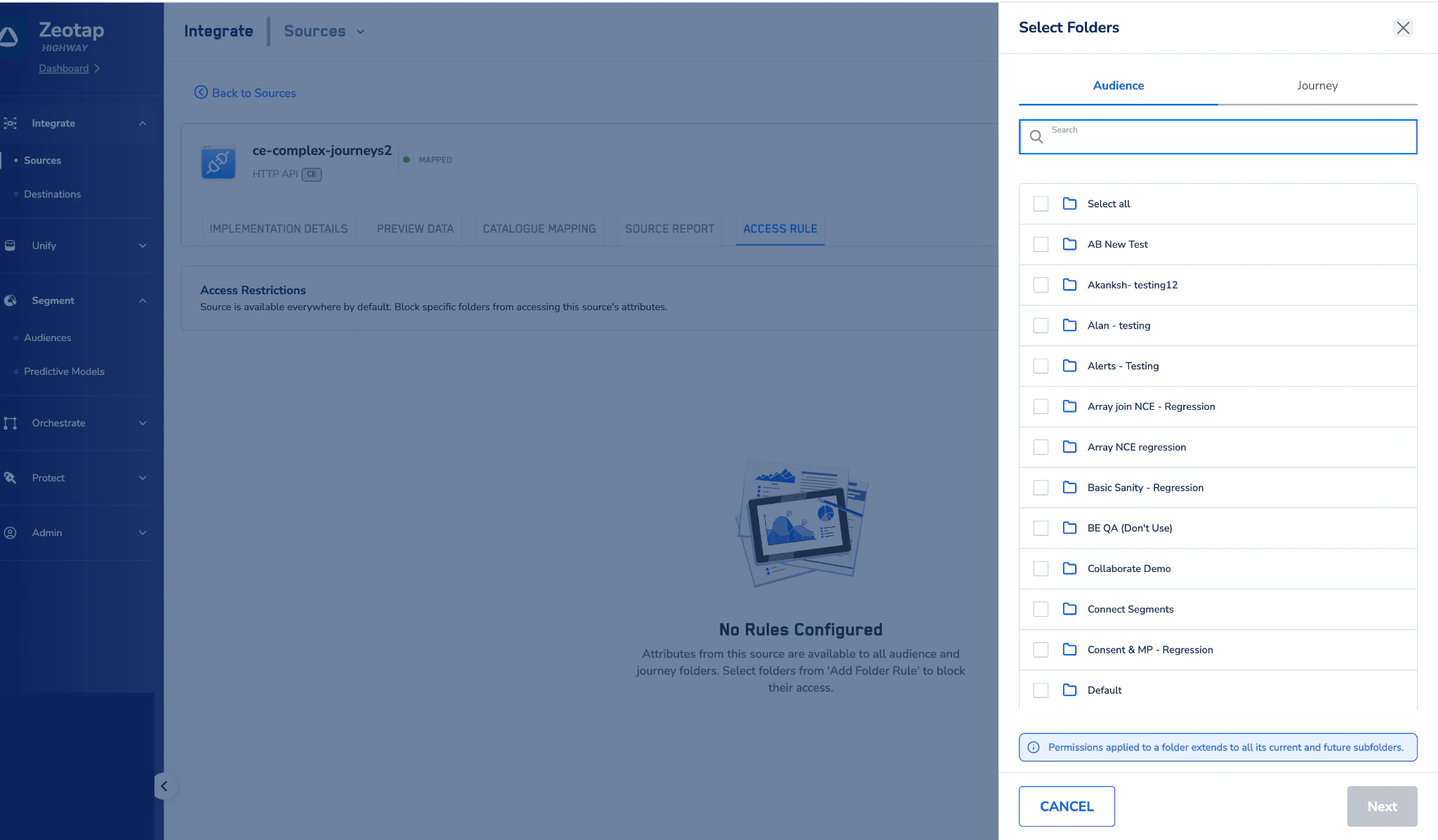
Click + Add Folder Rule and choose the audience and journey folders where the source (or specific attributes) should be blocked.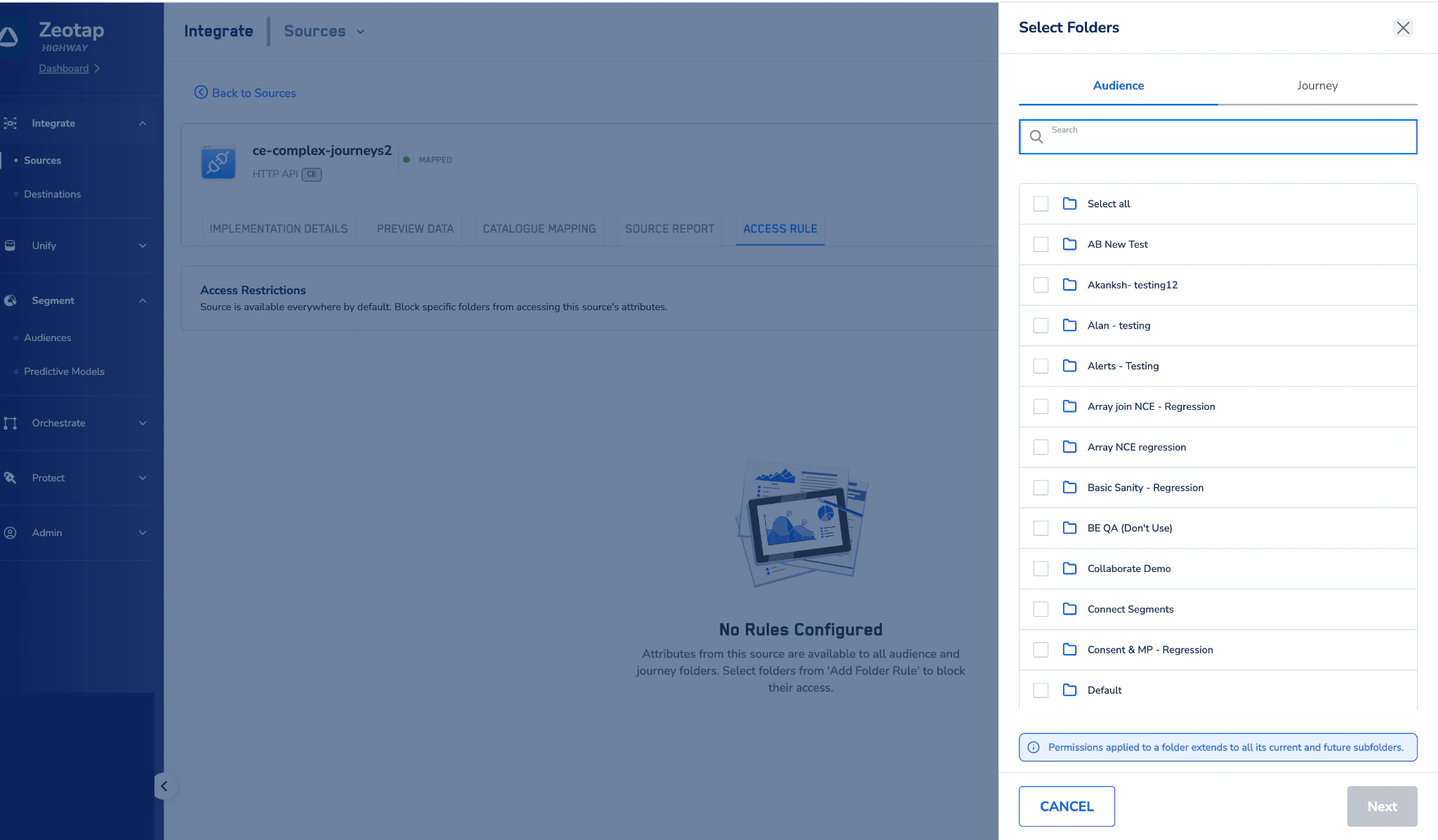
Select the attributes to block
Choose Select all to block every attribute from the source in the selected folders, or pick individual attributes to restrict access more narrowly.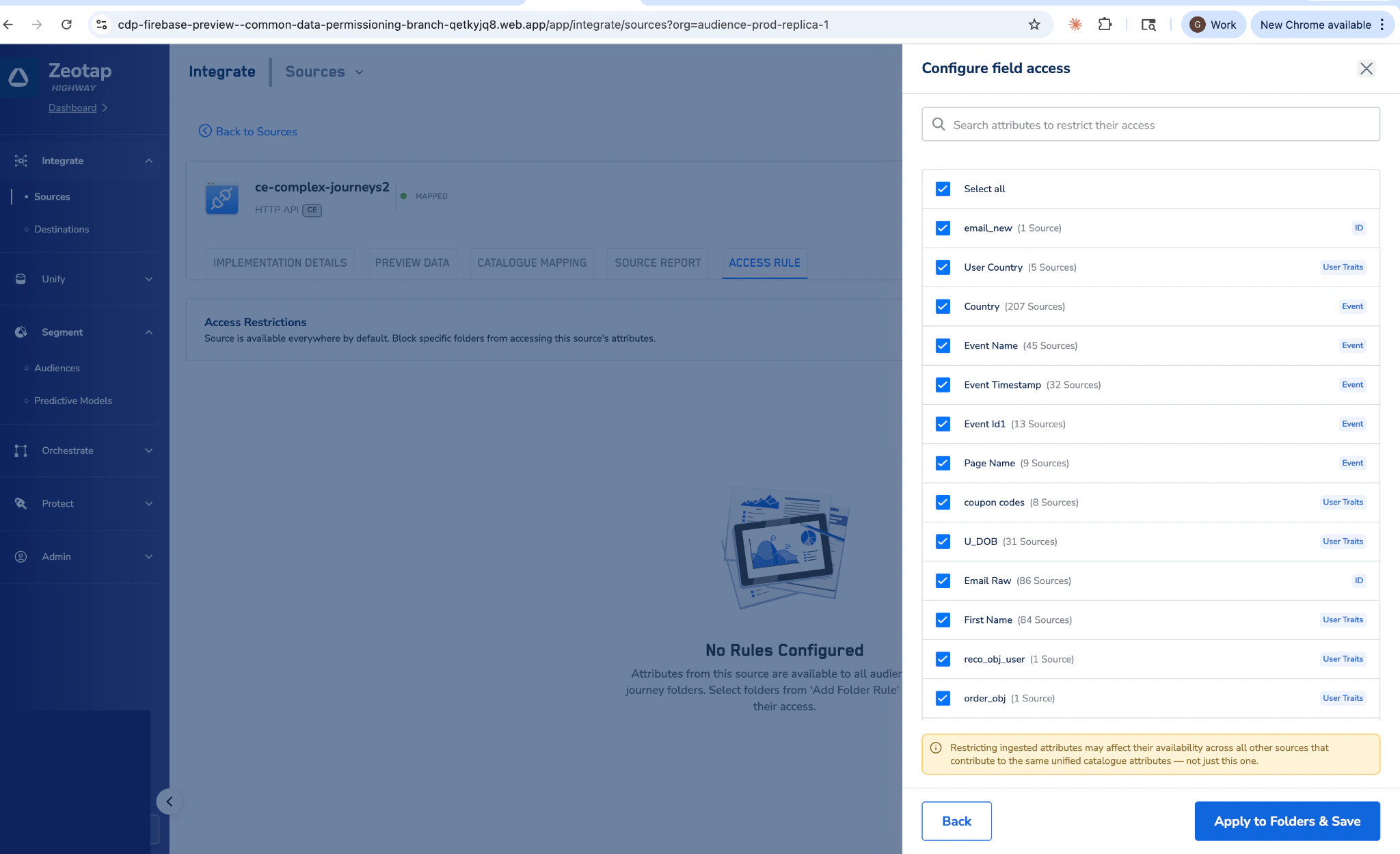
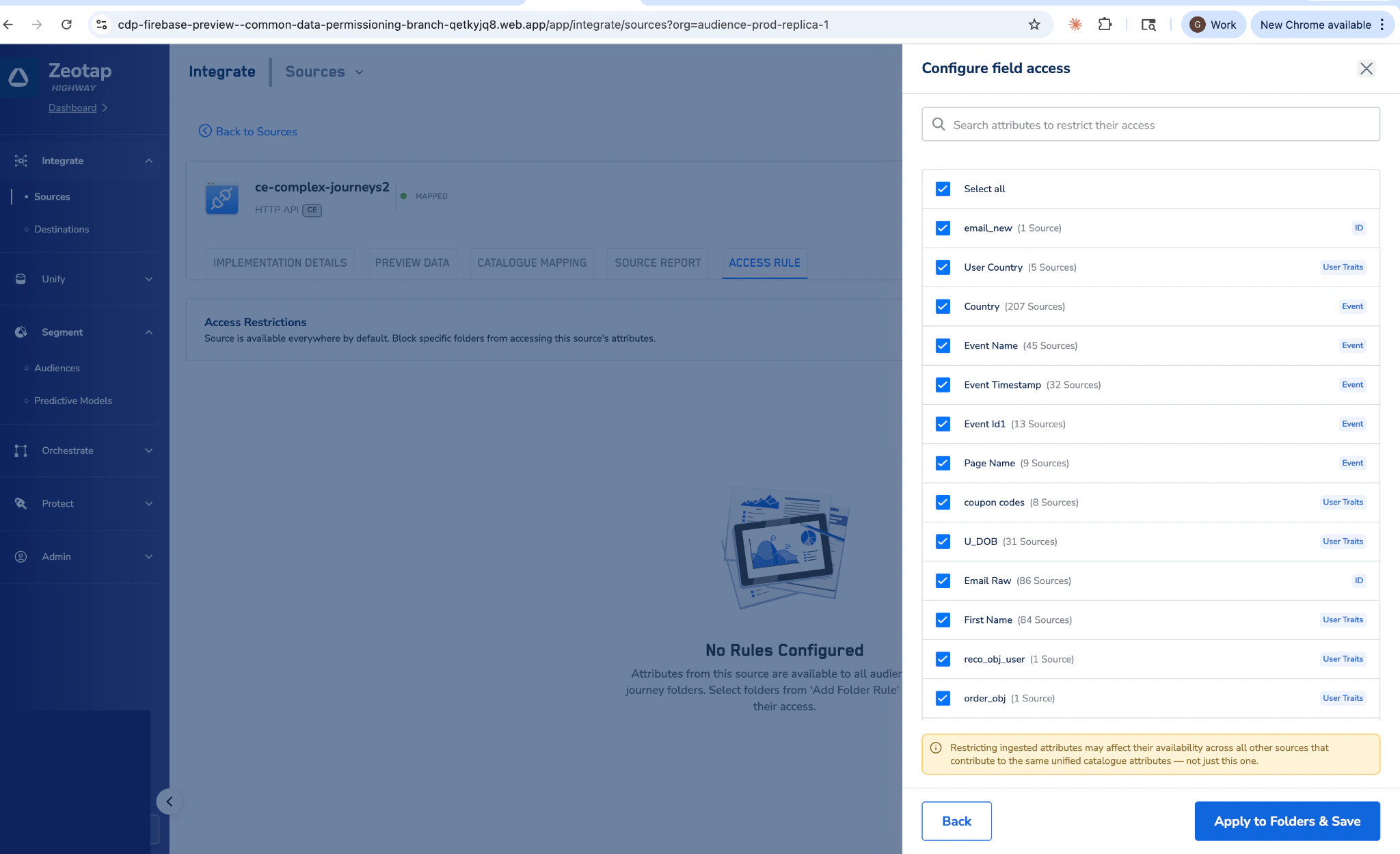
Review the impact warning
If the source contributes to any unified attributes, you’ll see a confirmation dialog calling out the cross-source impact before the rule is saved.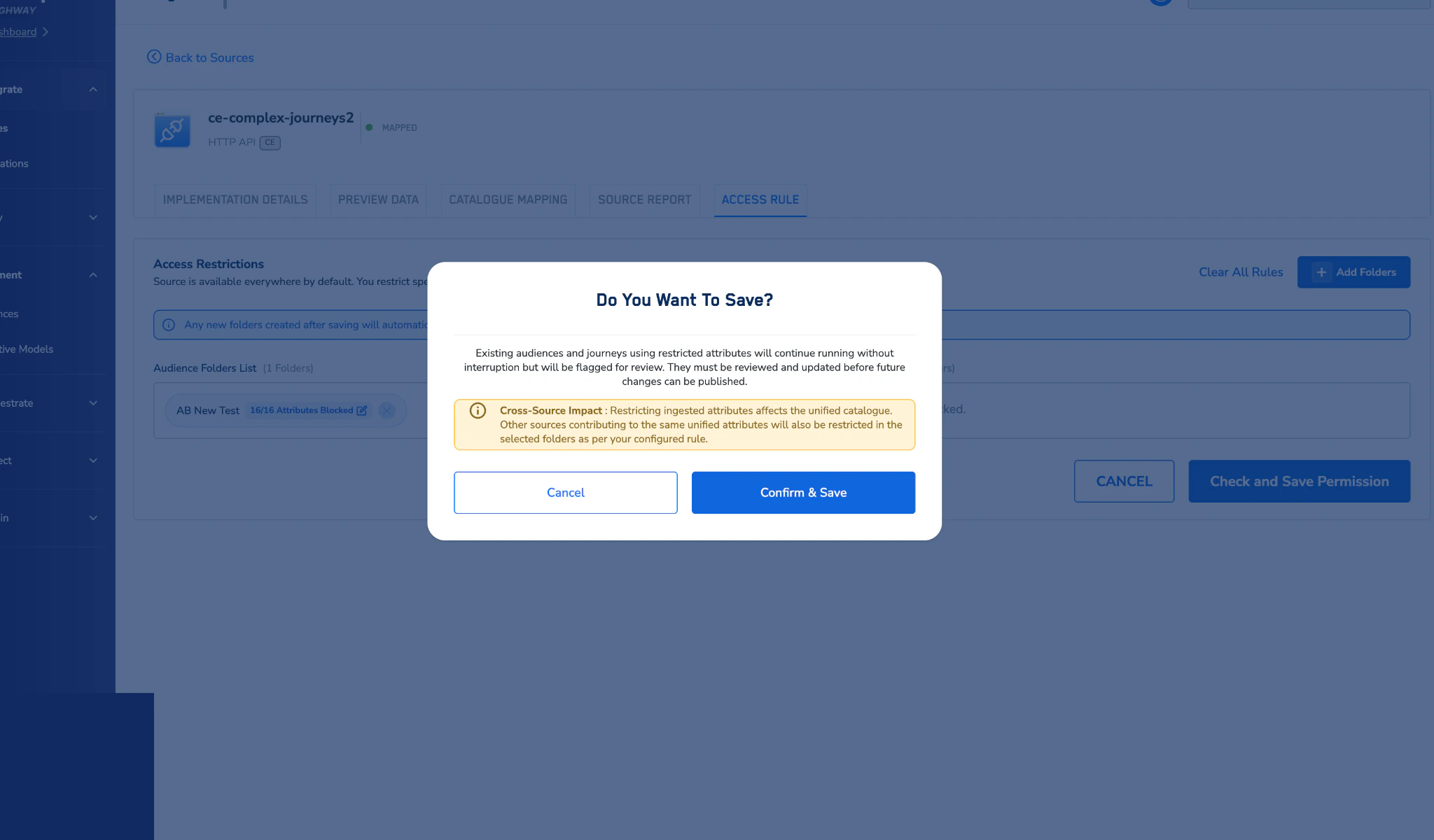
Edit an existing rule
Open the source's Access Rule tab
Navigate to Sources, open the source, and select the Access Rule tab.
Delete a rule
Open the source's Access Rule tab
Navigate to Sources, open the source, and select the Access Rule tab.
What users see when a source is restricted
In the Audience Builder
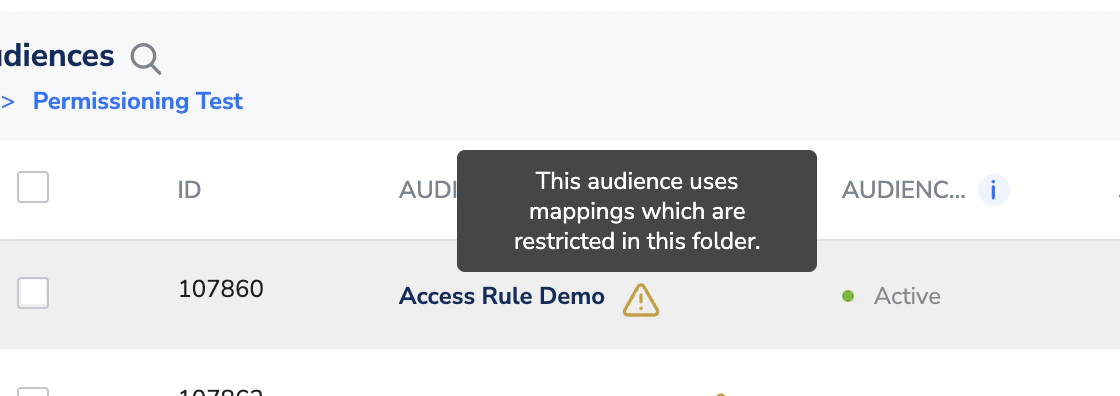
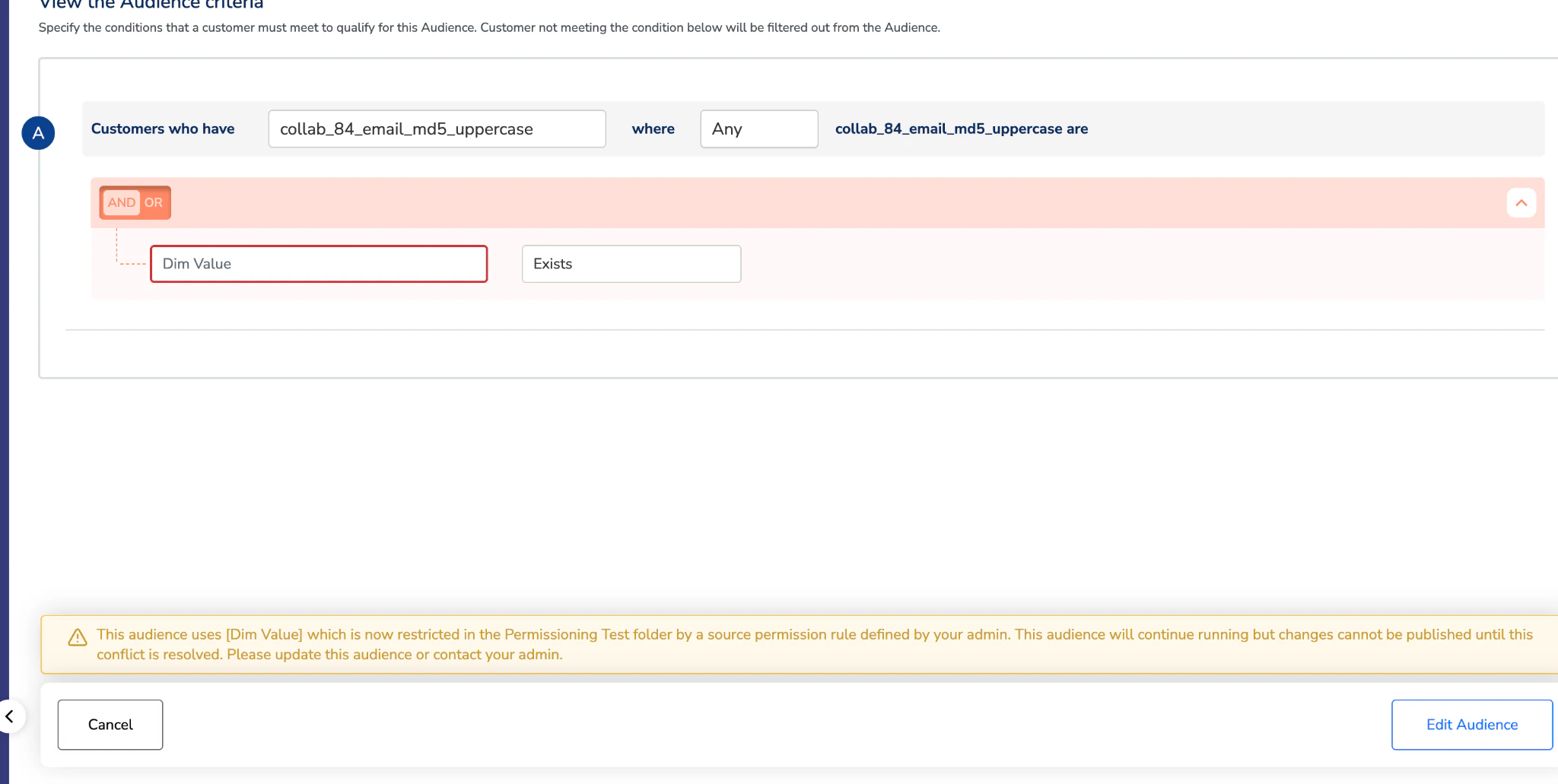
Blocked attributes are not available for selection — even if the source itself is otherwise accessible. Templates that use restricted attributes cannot be used either. Users also cannot send the restricted attributes to any destinations within the folder. Existing audiences affected by a new rule: Existing audiences continue running without interruption. However, any audience using a now-restricted attribute is flagged with a warning status on both the folder and the audience definition page.